It’s been a big week for WordPress security.
There have been several important security updates this week; including one that arose out of rather unnerving circumstances.
These updates make the WordPress space more secure, and participate (more broadly) in the ongoing battle for internet security.
Here’s an overview of this week’s security updates:
OpenSSL 1.0.1g
Monday, April 7
The week started in a state of panic when the infamous heartbleed bug was announced to the public. A computer security bug (aka heartbleed) has been targeting a security flaw in a widely-adopted security practice for over 2 years.
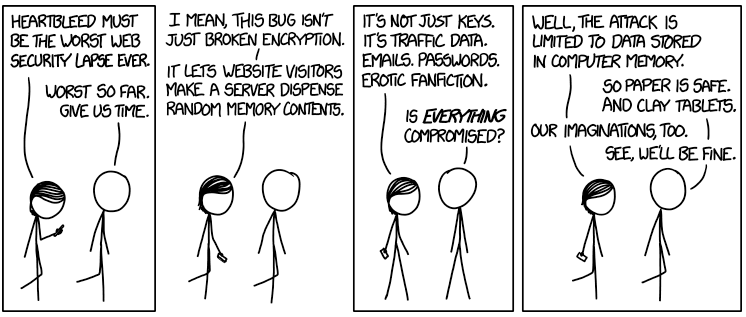
Heartbleed is unique in that it doesn’t target a specific operating system, but rather, it targets a vulnerability in a version of OpenSSL.
The vulnerability was identified several days prior to the announcement, allowing time for security engineers to mitigate the situation before alerting the public. Part of the alleviation plan was the release of OpenSSL 1.0.1g.
There are many sites that are running on a different version of OpenSSL, and are therefore not affected. Similarly, many sites have already implemented a security patch, and are no longer exposed to the bug.
A constantly updated ‘Heartbleed hit list‘ is available online. It includes information on which sites have been affected, if the vulnerability has been fixed, and more.
3.8.2 Security Update
Tuesday, April 8
Andrew Nacin announced the release of WordPress 3.8.2. The update provides a fix to several bugs, and contains security hardening changes.
Nacin expressed urgency for the update:
This is an important security release for all previous versions and we strongly encourage you to update your sites immediately.
3.8.2 provides a fix for site vulnerability to forged authentication cookies—a security concern discovered and fixed by Jon Cave.
The security release also provides extended privilege-setting abilities, which will prevent “Contributors” from publishing unapproved posts.
You can read more about the update here.
Jetpack 2.9.3
Thursday, April 10
The release of Jetpack version 2.9.3 addresses a critical security concern that was discovered during an internal security audit. The uncovered concern is a bug that enables attackers to bypass a site’s access controls and publish posts.
The vulnerability has existed since the release of Jetpack 1.9 in October 2012, but no evidence of its exploitation has been found. In the release announcement, George Stephanis said:
Now that this update is public, it’s just a matter of time before exploits occur.
The announcement went on to emphasize the seriousness of this concern, urging users to update their sites as soon as possible.
The update can be done through your dashboard. Alternatively, it can be manually downloaded.
Conclusion
It was quite an eventful week in terms of internet security! Happy Friday, everyone, and have a safe and secure weekend.
How were you affected by these announcements?
 Marie Dodson is an editorial assistant at Torque. She graduated from Cornell University with a degree in Biology and Society. She enjoys wine, good books, and travel.
Marie Dodson is an editorial assistant at Torque. She graduated from Cornell University with a degree in Biology and Society. She enjoys wine, good books, and travel.



No Comments