If you are anything like me, your website is like your baby. You put in a lot of effort, time, and often money to care for it the best way possible, make it user-friendly, and have it run smoothly. In addition to that, you do your very best to keep it from harm.
However, just like parenting, when it comes to website security, you won’t always get everything right. One hundred percent safety is just not achievable.
So, instead of trying to do everything right, how about concentrating on not screwing up completely? Avoiding the most common pitfalls can often be sufficient.
For that reason, in this article, we want to talk about some of most common WordPress security mistakes users make. By learning about them, you avoid committing them yourself. Doing so will make your website much safer.
Sound good? Then let’s dive right in.
WordPress Security Mistakes to Avoid at All Costs
Mistake #1: Shoddy Hosting
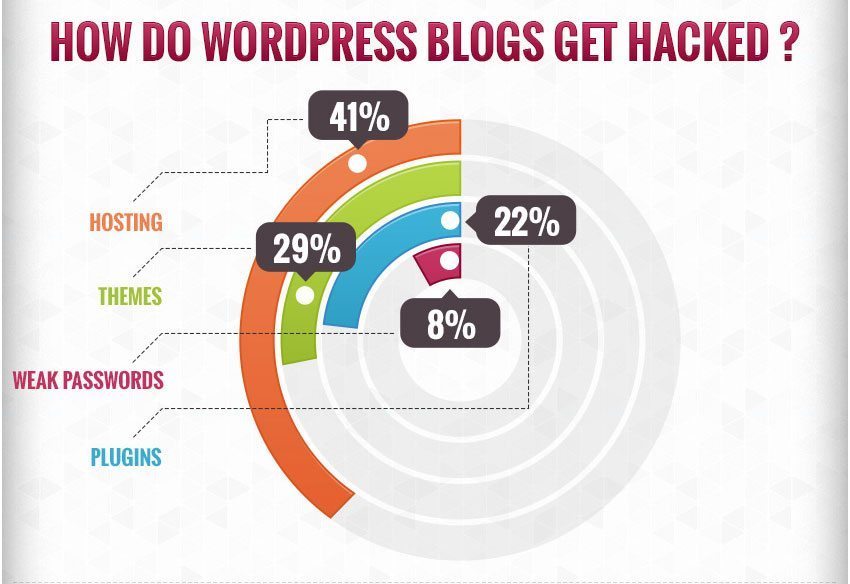
WordPress security starts with the hosting environment. In fact, according to WP Template, 41 percent of all website hacks happen due to insecure servers. That’s almost half! Crazy, right?
However, it highlights the need for quality hosting to make sure your site is secure.
Unfortunately, hosting is one of those areas where you get what you pay for. Most of the time cheap is cheap for a reason. With low-quality hosting, you often either have shoddy security to begin with or find a lack of support once stuff has hit the fan.
For that reason, consider hosting a business investment. Especially since for a hack to be successful, your site doesn’t even have to be the target. In a shared hosting environment, it’s often enough if one of the sites is compromised. Your site might just be taken down as collateral damage.
Mistake #2: Failing to Keep Up to Date
If you have been working with WordPress for a while, you will be aware that the platform is regularly updated. There are two different kinds of WordPress updates:
- Major updates — You can recognize those from their two-digit format, such as 4.6 or 4.7. They contain new features, code improvements, and a lot of other things including security updates.
- Minor updates — These come with a third digit (e.g. 4.7.2). Minor updates usually address smaller concerns, however, they also come as security updates if a vulnerability has been detected.
In both cases, it’s important to apply the updates as soon as possible. Doing so will ensure any vulnerabilities are patched.
Since WordPress 3.7, minor updates are implemented automatically unless you specifically switch this feature off. However, you can also enable the same for major versions. Just add the following to your wp-config.php file:
define( 'WP_AUTO_UPDATE_CORE', true );
Be aware though that major updates are more likely to cause conflicts with plugins and themes. For that reason, keeping the standard settings is more advisable.
Of course, what is valid for WordPress updates also applies to plugins and themes. In fact, vulnerable plugins and themes account for 51 percent of all hacked WordPress websites. Consequently, you’d do well to keep them up to date in order to minimize security risks.
Mistake #3: Using Insecure Login Information
Insufficient login security is another common WordPress security mistake. To understand why you need to know that most hacking attempts are automated. Nobody actually accesses your site and painstakingly tries out username and password combinations by hand.
Instead, they use automated scripts that can perform this action repeatedly in a shorter amount of time than any human ever could. However, many users also don’t put up much of a fight judging from the worst passwords of last year:
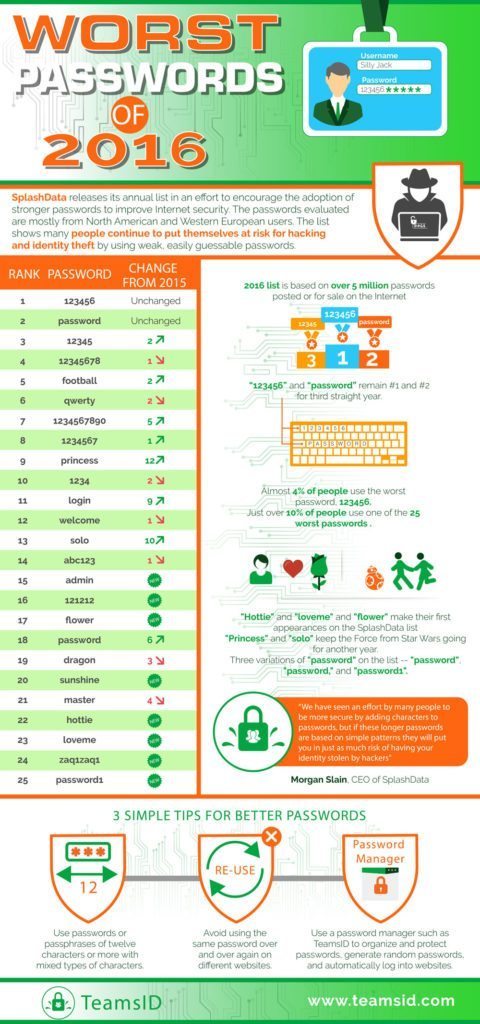
Here’s how to do better than the above:
- Limit the number of users with administration rights — WordPress has different levels of user roles for good reason. Not everyone on your site deserves to be able to do whatever they want. To make your site more secure, it’s a good idea to give everyone just as much permission as they need.
- Never use admin as a username — Admin used to be the standard WordPress administrator username, so it’s one of the first credentials hackers will try out. To make it harder for them, do not, under any circumstances, use it. If your site currently has an admin user, change it immediately!
- Use strong passwords — WordPress has had a password strength indicator for a while now and you’d do well to take advantage of it! Otherwise, use a service to create strong passwords for you (such as this one) and keep all passwords secure with a program like LastPass. Aside from that, this plugin will force others on your site to use strong passwords as well.
- Limit login attempts — To stave off brute force attacks, it’s a good idea to limit how often someone can try to log in to your site before being banned. Many security plugins offer this feature but you can also use Login Lockdown and WP Limit Login Attempts to add it.
- Hide the login page — For extra security your might also consider moving your login page to an unfamiliar location. A plugin with this ability is Move Login.
Mistake #4: Installing Themes and Plugins from Untrustworthy Sources
The popularity of WordPress has made it a favorite target for hackers. However, not all sites are compromised from the outside. Often, it’s the site owners themselves that do the compromising.
One of the most common ways of that happening is by installing “free” WordPress themes and plugins that, while they don’t cost money, come with other costs.
A few years ago CodeinWP published the aptly named article WordPress Free Themes – Don’t Use Them. They tested many of the themes freely available on the web and found lots of exploits, malicious JavaScript and other problems.
For that reason, you’d do well to stick with trustworthy sources. First and foremost that means the WordPress directory. Here you can find free WordPress themes and plugins that have all been vetted for quality.
Aside from that, there are a number of trustworthy third-party vendors. This list is a good start to find them. Meanwhile, Google has also gotten much better at showing reliable results to people searching WordPress themes and plugins. However, it’s still advisable that you proceed with caution.
Mistake #5: Hoarding Unused Plugins, Themes, and User Accounts
Non-harmful WordPress accessories can also be a security risk, especially if you don’t update on a regular basis. For that reason, to minimize the risk, minimize their number.
When running your site for a long time, it’s common to accumulate unused themes and plugins. Deleting them makes sure none of them can become a security risk. In addition to that, purging your site of unnecessary clutter is a great way to reduce requests at page load and thus speed up WordPress.
What’s true for themes and plugins also applies to user accounts. Every user account is a possible gateway for a hack. The less you have of those the better. So, if any user account is not necessary anymore, feel free to delete it (after assigning the content to another person).
For more tips on this topic, check out this WordPress spring cleaning guide.
Mistake #6: Failing to Back Up Regularly
Even if you take all possible security measures, no site can ever be a hundred percent secure. Bad things happen for a number of reasons and not everything is under your control (such as your hosting environment).
For that reason, it’s super important to regularly create copies of your website. That way, in case something goes wrong, you can always go back to a working site version.
If you are using a quality host (see mistake #1), they will create daily backups for you. However, to be extra cautious, you should also implement your own backup solution. Here are just a few that you can choose from:
Pick your favorite, set it up now and thank me later.
Mistake #7: Not Using WordPress-internal Security Measures
WordPress itself comes with security measures built in. However, in some cases, you need to take action to take advantage of them.
One such example is the database prefix. By default, it is set to wp_. However, since this is public knowledge, going with the standard settings makes you more vulnerable for SQL injections.
As a consequence, it’s a better idea to change it to something random that’s hard to guess. You can either do so at installation or, if your site is already set up, with a plugin like iThemes Security. Aside from that, there is also a manual method.
Secondly, there are SALTs. These are security keys that are added to wp-config.php. They are used to encrypt information stored in cookies to keep your site safe. The keys belong inside the file where it says:
define('AUTH_KEY', 'put your unique phrase here');
define('SECURE_AUTH_KEY', 'put your unique phrase here');
define('LOGGED_IN_KEY', 'put your unique phrase here');
define('NONCE_KEY', 'put your unique phrase here');
define('AUTH_SALT', 'put your unique phrase here');
define('SECURE_AUTH_SALT', 'put your unique phrase here');
define('LOGGED_IN_SALT', 'put your unique phrase here');
define('NONCE_SALT', 'put your unique phrase here');
Use the SALT generator to create your own set and replace them. Just click the link above, copy and paste. Done.
Mistake #8: Not Using a Security Plugin
In case you don’t feel capable implementing the tips above on your own, the worst mistake would be to not take action at all. Several high-quality security plugins out there can assist you in making your site bulletproof without technical knowledge. Here are the main contenders:
They can do many of the things we talked about above. Consequently, if you are less technically inclined, take advantage of the help.
WordPress Security Mistakes in a Nutshell
Having your site hacked or taken down sucks. Seeing the fruit of your effort, time, and money disappear is a real nightmare. The good news, however, is that situations like that can usually be avoided by addressing common WordPress security mistakes from the beginning.
In the article above, we have looked at a list of things many people get wrong about WordPress security. From bad hosting, failing to update and insecure login information, to untrustworthy or excessive themes and plugins, lack of backups, and other security snafus.
By avoiding the mistakes above, you can give your site the best chances to stay unaffected by security concerns. If something does happen, you still have our article on how to recover a hacked website to get you back on track. However, the chances are slim that you will have to use it.
What about you? What WordPress security mistakes have you made in the past? Anything to add to the above? Let us know in the comments section below!

10 Comments