This past Valentine’s Day, millions of friendly and romantic email messages were exchanged around the world. Unfortunately, some of them were exploited by cybercrime groups aiming to infect personal computing devices and networks with GandCrab ransomware.
Information security researchers at Mimecast Threat Labs noticed a considerable uptick of activity in the world of Ransomware-as-a-Service (RaaS), a cybercrime business model that has been on the rise for nearly a year. More interesting, perhaps, are emerging details surrounding this threat.
eMafioso?
The rise of RaaS is one of various turning points in the cybercrime world, which is starting to show parallels with the way other criminal organizations have historically developed. In the recent trial of Joaquin “Chapo” Guzman, former leader of the Sinaloa drug cartel, analysts remarked that the organization itself was hardly affected by the sentencing of the crime lord in a New York courtroom because it has been operating as a resilient global business for decades.
In fact, the Sinaloa cartel has been shifting its profit-making activities from drug smuggling to illegal mining and fuel theft in Mexico. Major cybercrime groups have adopted this business-like resilience with RaaS, a subscription-based modus operandi that features access to ransomware packages that criminals can use even if they are not familiar with coding malware apps.
Ransomware, Inc.
Affiliate programs and marketing campaigns are now part of RaaS, which explains why sales of the ransomware increased in the run-up to Valentine’s Day. Cybercrime outfits offering RaaS launched a creative marketing campaign that included ideas on how prospective criminals could make the most out of the Feast of Saint Valentine, particularly in the United States. Some of the topics and attack vectors promoted were:
* Fake dating apps.
* Trojan horse greetings that would redirect victims to websites where they would be injected with GandCrab ransomware.
* Fake internet surveys designed to capture personal data from victims.
* Spyware that would exchange web advertising banners with malicious versions.
The aforementioned marketing campaigns were launched across dark web marketplaces, encrypted messaging apps, and underground internet forums. To get an idea of how sophisticated these cybercrime groups have become, an efficient ransomware package such as Hostman, which features Bitcoin payment processing and even automatic decryption of files for victims who comply with the terms of the ransom note, costs $49.95 for unlimited use. Just like many information security systems are now cloud-based, so are the attackers.

Politics and Patriotism in the RaaS World
One of the most interesting findings reported by Mimecast Threat Labs researchers is that the GandCrab RaaS campaign launched ahead of Valentine’s Day was mindful of not targeting Russian users. Should the malware app detect a Cyrillic keyboard or a Russian language pack configuration in the operating system, the attack would not be carried out.
That major ransomware crews operate out of Russia is a known fact, but why should cybercrime operators care about not targeting their own people?
It so happens that the geopolitical state of affairs has a lot to do with the way cybercrime groups operate. We already know that Russian hacking outfits have worked with the Kremlin and intelligence agents to interfere in international elections.
It is likely that this partnership requires cybercrime groups to refrain from attacking friendly targets. To historians, this is hardly surprising; after all, the Sicilian mafia was known to form political and religious partnerships during the 1970s and the 1980s.
Political and patriotic sentiment can influence the actions of malicious hackers and organized crime groups alike. In some cases, criminal organizations recruit hackers for the purpose of diversifying their operations and pursuing political activities.
Earlier this year, Roberto Escobar launched a cryptocurrency based on the Ethereum blockchain, and he made it clear that profits would be used to fund lobbying and investigative efforts to impeach U.S. President Donald Trump. Roberto is the surviving brother of Pablo Escobar, the notorious leader of the Medellin Cartel, who was gunned down in Colombia with the help of American law enforcement in 1993.
Ransomware Decryptors to the Rescue?
No one is safe from ransomware attacks, not even victims of the protracted Syrian conflict. In October 2018, a heartbreaking Twitter update from a Syrian man explained that his computer had been infected with GandCrab version 5.0.3, and he was at risk of losing images and videos of his children, whom he lost in the conflict.
Amazingly, a group behind the GandCrab RaaS operation learned about the plight of Syrian victims and reached out to key members of underground hacking forums for the purpose of releasing a decryption tool specifically for this affected group. This “decryptor” was evaluated and modified by the ESET information security firm for the benefit of all GandCrab victims.
Law enforcement agencies in various countries have been releasing decryptor variants for individuals and companies that have been hit with GandCrab ransomware. As can be imagined, this has been a major setback for some RaaS operators, who are currently working on future versions of their software that would be impervious to these decryption tools. In the meantime, however, email scammers have been taking advantage of this positive development.
No Malware Needed
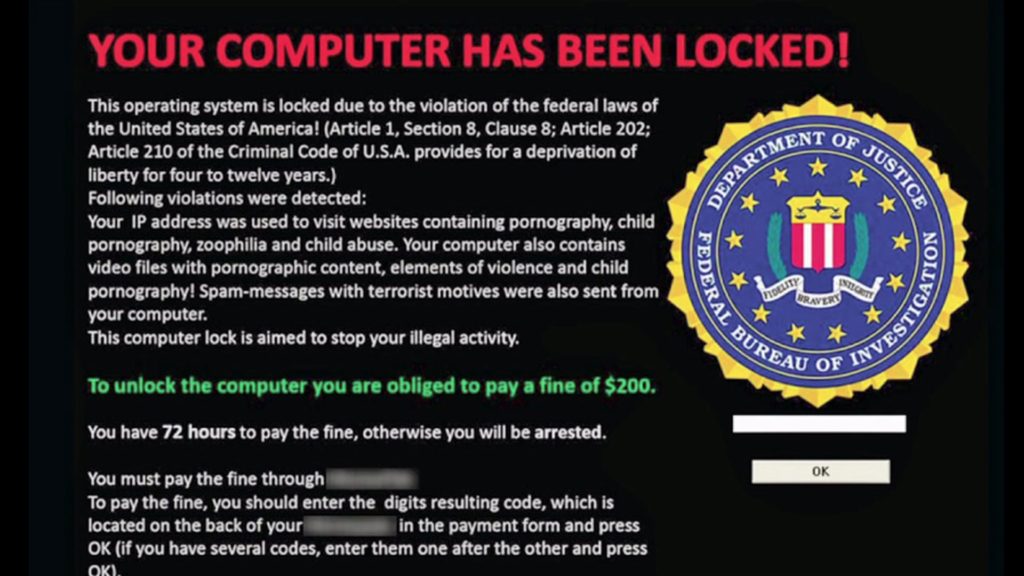
Researchers at Cyber security firm Sophos Labs have intercepted emails that feature a “reverse engineering” approach to ransomware attacks. In essence, the scam is a type of protection racket insofar as victims being made to believe that they have been infected with ransomware.
The body of the email is a lengthy and intimidating ransom note directing recipients to make a cryptocurrency payment of about $600 to avoid activation of the non-existing malware.
In some cases, the messages include links to news stories about the previously mentioned decryptor efforts in Europe. Other emails simply offer decryption tools, which are available, for a price.
Many of the recipients have been small companies, which leads investigators to believe that marketing email lists may have been hacked in this attack; to this effect, small business owners are urged to carefully evaluate their email marketing services providers. In the end, the best strategy to protect against ransomware attacks continues to be comprehensive data backups.
The Bottom Line
“Life finds a way.”
This line so eloquently rendered by Jeff Goldblum in Jurassic Park could be applied to the hacking world as well, maybe something like, “Cybercriminals find a way.” One thing is certain. For every bit of good in this world, expect that there will be a certain human element completely dedicated to tormenting, perverting, and making a profit. So…be careful out there.

1 Comment