Website security: two words that should be of paramount importance for all site owners. Security is big business online, mainly because it’s so vital that to ignore it can mean catastrophic consequences for your website and its user base. However, some security issues are more pertinent than others – and figuring out what’s most important to focus on is a task with no clear starting point.
Fortunately, the Open Web Application Security Project (OWASP) exists to help improve software security. Recently, this organization published an invaluable top-ten list of security vulnerabilities from the past year (2017). This can give you a valuable head start when it comes to keeping your site, as well as the data it collects, safe and sound.
In this post, we’ll examine these top ten security risks, and outline what you can do to minimize their impact (or eradicate them if possible). However, first let’s take a quick look at OWASP and what it does for online security!
An Introduction to the OWASP
The Open Web Application Security Project (OWASP) is an open-source, not-for-profit organization, committed to helping increase the security of the software we use daily. It’s been active since 2001, and its staff is widely considered to be experts in their field.
OWASP produces its top ten security vulnerabilities on a yearly basis, but that’s not all it does. There are a number of other active projects it runs that concern security. For example, it offers the:
- WordPress Security Implementation Guideline. This is a comprehensive and constantly-updated guide to making sure your WordPress installation has watertight security. It’s a useful tutorial for preventing malicious intrusions.
- WordPress Vulnerability Scanner. This tool detects any weak links in your WordPress installation, enabling you to fix them and protect your site from attacks.
You can check out a full list of OWASP projects on the organization’s website. For this piece, however, we’re going to focus on the yearly top ten security risks.
A Breakdown of the OWASP Top 10 Application Security Risks for 2017/18
Assimilating the contents of this top ten list is vital for keeping your website secure. Not paying attention to each risk could lead to intrusions, compromised data, or much worse. We’ll present the list in order from the biggest threat to the least important one (although all are worth paying attention to). Let’s take a look!
1. Injection Flaws
Injection flaws occur when untrusted data is sent as part of a command or query. You’ll find that SQL injection is most common, although other types do exist. In some cases, un-sanitized user data is an entry point, which makes this vulnerability wide-ranging and dangerous.
As you can imagine, the WordPress team takes this issue very seriously. Developers have a set of functions and APIs to help increase protection from unauthorized code injections, as well as to sanitize data correctly. Some users have also gone as far as restricting file type uploads and sizes, which (depending on your needs) can be a smart idea.
2. Authentication Issues
If administrative accounts fall into the wrong hands, attackers can easily compromise user credentials, such as usernames and passwords. This usually occurs when authentication and session management solutions are implemented incorrectly.
As you may imagine, solving this issue relies heavily on the user in question, although there are things an administrator can do as well. For starters, choosing a solid password is a must, as is setting up multi-factor authentication. Finally, a plugin such as WC Password Strength Settings will help you force users to choose strong passwords.
3. Exposing Sensitive or Personal Data
This vulnerability is very similar to the previous one, although it concerns compromises to user-inputted data. Think about how catastrophic exposing details such as personal addresses and payment information can be – not only for customers but for the business itself.
Fortunately, WordPress provides defenses against this risk out of the box. For example, passwords are salted, hashed, and made strong via the built-in password generator. What’s more, the permissions system takes care of most other entry points.
To heighten security further, you can encrypt data by implementing Secure Sockets Layer (SSL). We’ve previously talked about how to do this, using the open-source and free solution Let’s Encrypt.
4. XML External Entities
This next vulnerability might sound dauntingly complex, so we’ll try and keep the description simple. Essentially, this is an injection-style attack carried out through malicious code, within Extensible Markup Language (XML) files.
The first fix is to simply use a less complex data format than XML where possible (JSON, for example). WordPress actually disables custom XML entities from loading, to help prevent attacks. You can find out more about this complex issue (and how to fix it) directly from OWASP.
5. Broken Access Control
Much like our earlier discussion about authentication, access controls (i.e. controls that determine user permissions) can also become broken. Of course, a user without correct permissions (more specifically, with more permissions than they should have) could wreak havoc.
Once again, WordPress is coded to help ensure that this issue doesn’t occur. The platform checks for proper authorization before a request is carried out (especially for ‘function-level’ access controls). While this risk is part of the top ten, it’s something you’ll rarely have to worry about.
6. Misconfigured Security
Misconfigured security issues can be code-related, but you’ll often find that this vulnerability occurs due to user error. Regardless, the consequences are much the same as with other permissions-based vulnerabilities.
The good news is that you can address this risk in a number of simple ways. For example, basic WordPress security – such as not using default usernames and keeping themes and plugins up to date – will protect you. For further peace of mind, you may want to carry out some advanced hardening of WordPress.
7. Cross-Site Scripting (XSS)
Given how much content exists about Cross-Site Scripting (XSS), you’d be forgiven for thinking that it should be higher on this list. It’s part of the ‘injection’ family of vulnerabilities, taking advantage of dynamic site elements to hijack the user’s browser and computer. As such, making sure it’s not an issue is vital for trust and ongoing good relationships with your users.
Given the impact of XSS, WordPress developers work under the hood to make sure that users are protected. For example, content submitted by untrusted users (i.e. those who are not Administrators or Editors) is filtered by default. What’s more, there are a number of functions available to help WordPress developers with validation and escaping of user data.
8. Insecure Deserialization
This is another complex vulnerability. In short, untrusted data that is being serialized and deserialized is potentially open to exploitation, which can result in data being exposed. This type of data includes caches, databases, API authentication tokens, and more – all common elements of modern WordPress websites.
During our research for this article, we found no real instances of this vulnerability causing problems in the past. That doesn’t mean it should be ignored. In our opinion, however, the fact that we found no examples of this issue is a testament to WordPress’ inherently secure nature.
9. Insecure Themes, Plugins, and Other Components
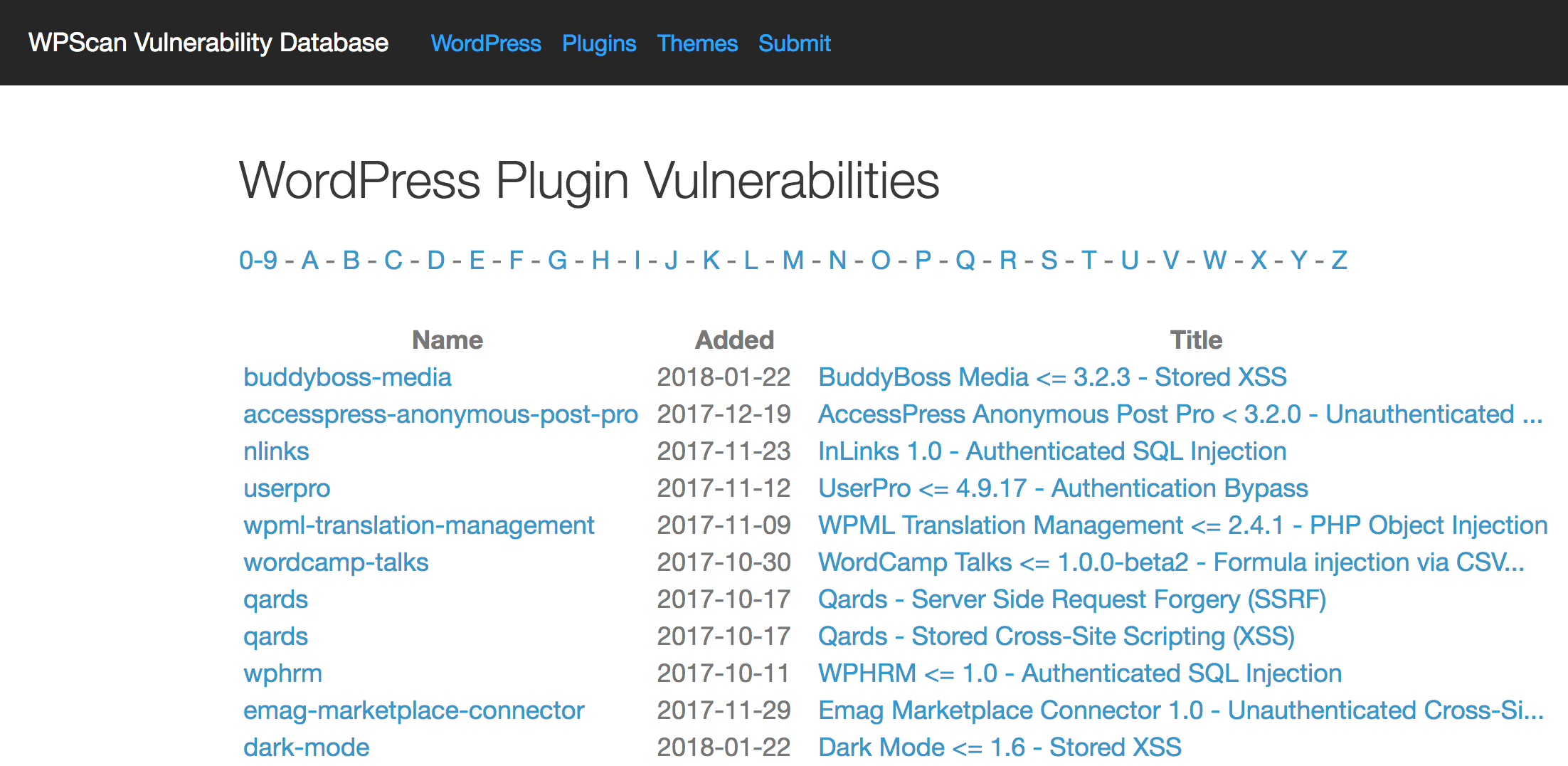
It’s easy to forget that many elements of WordPress – themes, plugins, etc. – can potentially compromise your site. Any of the vulnerabilities on this list can be caused by a poorly coded theme or plugin, so extending your concerns to the tools you’re using is crucial.
Fortunately, plugins and themes found in WordPress’ directories have already been checked for quality, so they shouldn’t cause problems. However, this quality assurance isn’t foolproof. We recommend carrying out a thorough check of your own, using a site such as WPScan’s Vulnerability Database, before installing any tool on your site:
For additional peace of mind, WordPress also monitors the libraries and frameworks it contains for exploits. In some cases, it will patch third-party tools to help keep users safe.
10. Insufficient Logging and Monitoring of Your Site and Its Data
Our final vulnerability isn’t actually a direct exploit, although it can do just as much harm to your website. If you fall victim to any of the above vulnerabilities, you may not even be aware of it if you aren’t monitoring and logging what happens on your site. This leaves your site open to even more malicious attacks and can erode any trust you’ve gained with your user base.
This is a subject we’ve touched on before when talking about how to comply with the General Data Protection Regulation (GDPR). Ultimately, using a quality security logging plugin such as WP Security Audit Log should be a priority:
This plugin logs practically every action taken on your website, and should become a central component of a regular security routine. In a nutshell, if an action looks out of place in the log, investigating it thoroughly can unearth any exploited vulnerabilities. This means you can deal with them before they result in catastrophe.
Conclusion
Security should be of paramount importance for any website admin. However, knowing which areas to pay the most attention to can be tough – and if you choose poorly, the consequences could be severe for both you and your users.
The OWASP initiative comes to the rescue on this front, as this organization produces an annual report breaking down the top ten vulnerabilities you should pay attention to. For WordPress users, many of these risks can be contained using plugins such as Wordfence and WP Security Audit Log. Others (such as not using insecure themes and plugins) are solely down to you and your conscientiousness. Either way, keeping tabs on these security risks should be an ongoing concern.
Do you have any questions about the top ten security vulnerabilities and how they can affect you? Let us know in the comments section below!
Featured image: TanteTati.

No Comments