If you run a WordPress site, you might be aware of the many security risks that could threaten your business. For example, Remote Code Execution (RCE) attacks can exploit your website vulnerabilities to steal data, destroy your content, or take over your site altogether.
Fortunately, you can easily protect your website by understanding the ins and outs of this kind of attack. With proper knowledge, you can take the necessary steps toward securing your website against RCE hacks.
In this post, we’ll discuss RCE attacks and how they can harm your website. Then, we’ll discuss five ways you can protect your site, including using a Web Application Firewall (WAF). Let’s dive right in!
An Overview of Remote Execution Attacks
RCE is a cyber-attack where a hacker remotely executes code commands on somebody’s device. These attacks may happen if the host unknowingly downloads malicious malware. Then, the hacker can install data-stealing malware and deny access to user files until the owner pays a ransom or mines cryptocurrency.
Furthermore, once an attacker has exposed a vulnerability, they can exercise complete control over your information and device. Your customer data may be compromised, you might lose your website files, and your reputation can be destroyed forever.
Moreover, RCE attacks are increasing, rising from 7 to 27 percent of the most common critical vulnerabilities between 2019 and 2020. This increase is likely due to the COVID-19 pandemic moving many businesses to a virtual-first environment.
How to Protect your Website Against Remote Code Execution Attacks (5 Ways)
We’ve just covered the dangers of RCE attacks. Now, let’s discuss five ways to protect your website from them!
1. Install a Web Application Firewall
A Web Application Firewall (WAF) is an excellent prevention tool that can protect your site against various security risks, including RCE attacks. It monitors and filters HTTP traffic to block suspicious parties from breaching your defenses. Essentially, it acts as a buffer between your web server and incoming traffic.
For example, a tool like Sucuri WAF can safeguard your site against RCE attacks, speed up your loading times, and even increase your website’s availability:
In addition to protecting your site against RCE attacks, Sucuri can remove existing malicious code on your site and prevent DDoS attacks. Depending on your web host, your hosting service might also come with WAF protection.
2. Ensure Your Software Is Up-to-Date
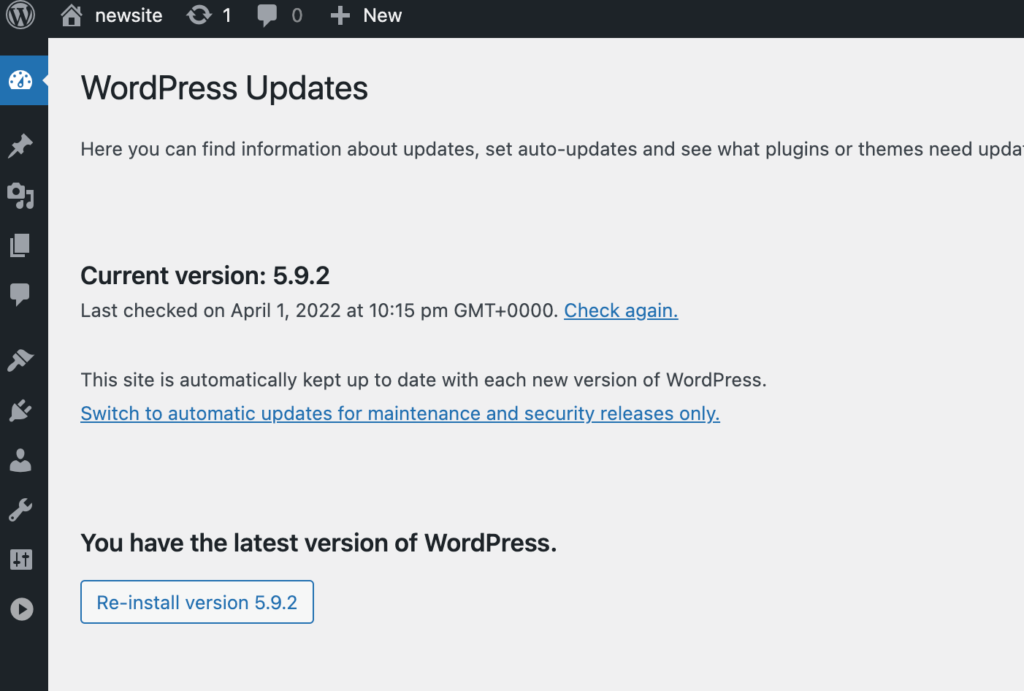
Keeping all your website software up-to-date is critical for RCE prevention. Therefore, it’s crucial to consistently monitor your site for new updates to themes, plugins, and the core WordPress software.
The developers behind WordPress, plugins, and themes regularly roll out updates that improve security and functionality. Thus, updating your site as often as possible effectively minimizes security risks that RCE hackers could exploit.
Head to Dashboard > Updates in your WordPress dashboard to manually update your software. Here, you can view any available updates and enable them by clicking on them:
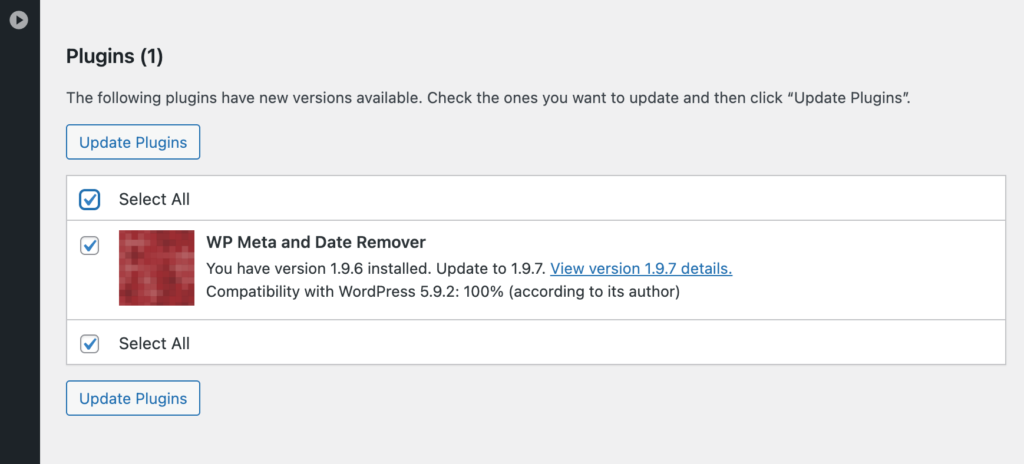
If you have any outdated plugins, click on Select All and Update Plugins to get to the latest versions:
Alternatively, you can partner with a managed WordPress hosting provider. This company takes care of multiple behind-the-scenes tasks like automatic updates, website security, and performance boosts. Choosing a managed host can automatically protect your site against RCE attacks and other security threats.
For example, WP Engine is a reliable web host with a sophisticated WAF, automated updates, daily backups, and access to both a Content Delivery Network (CDN) and SSL certification:
WP Engine hosting plans start at $23 per month. This package supports one website and 25,000 monthly visitors.
3. Use Buffer Overflow Protection
A buffer holds data in a memory storage zone while it is transferred between different locations. Overflow happens when the amount of data is more than the buffer’s capacity. When this happens, the data-writing program starts overwriting other memory locations.
If there is a buffer overflow, it can enable exploiters to overwrite your software’s memory. They can add malicious code and commit an RCE attack. Therefore, protecting your site against buffer overflow is critical to preventing RCE threats.
Fortunately, buffer overflow protection is typically built into most theme code libraries in WordPress. Languages such as C/C++ may not have buffer overflow protection, but Javascript, PERL, and C# do.
Therefore, we also recommend following coding best practices to protect against buffer overflow when developing your site.
4. Limit User Access Permissions
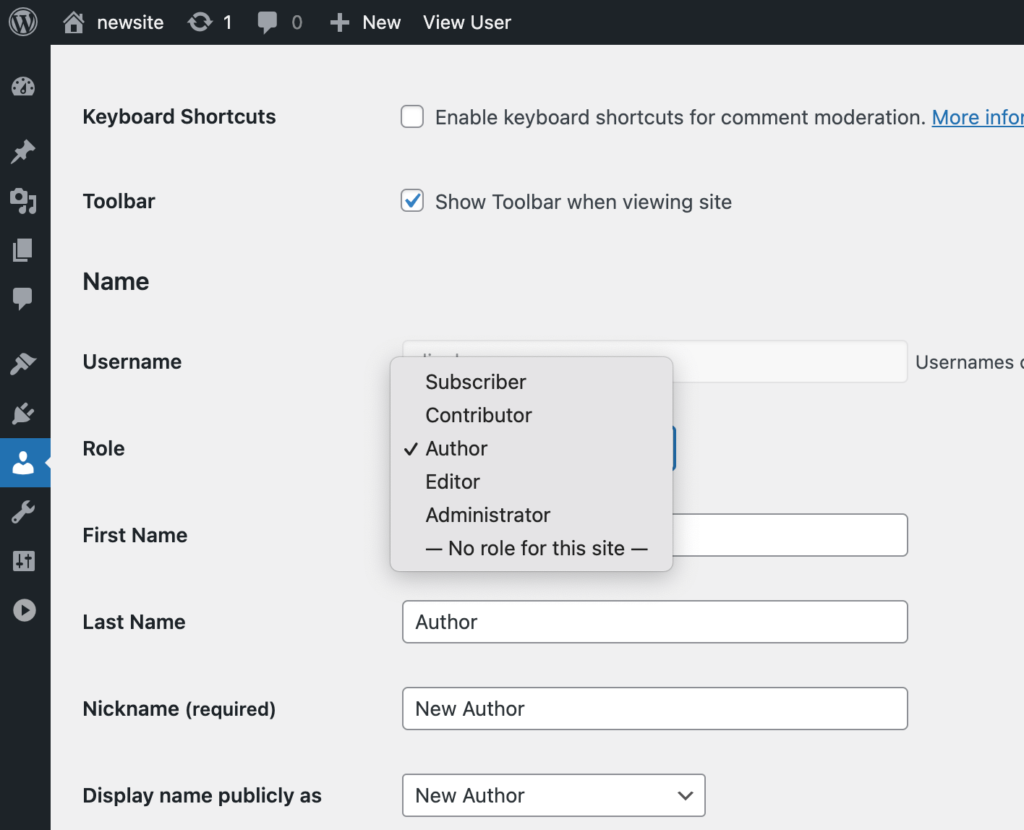
In WordPress, you can assign multiple different permissions to your users. For example, there are administrators, editors, authors, contributors, and subscribers. Each user type has different permissions, and only the administrator can directly edit the code.
By ensuring each user only has the access level they need to do their job, your site won’t be fully compromised if a hacker infiltrates one of the user roles.
For example, if you have freelance writers on your blog, consider assigning them as editors, authors, or contributors, depending on their roles.
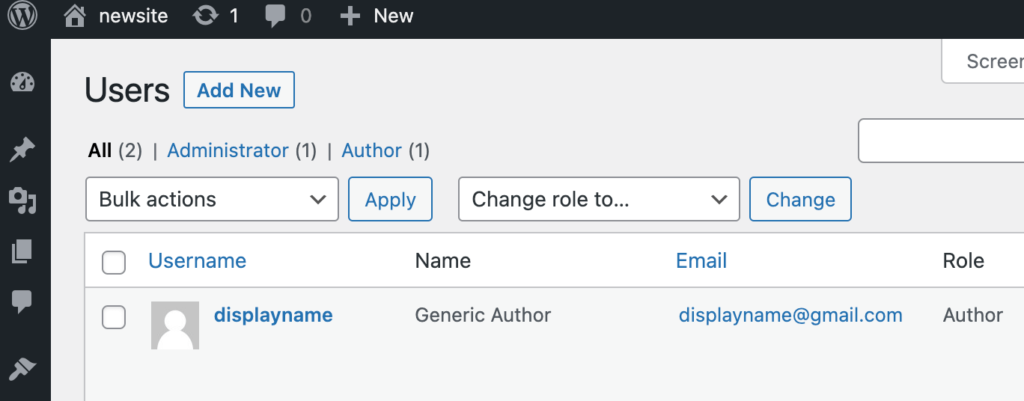
Navigate to Users > All Users in your WordPress dashboard to edit user roles. Then, click on Edit under the user you want to modify:
Then, scroll down to Role and select an appropriate role for the user from the drop-down menu:
As a general rule, don’t give anybody the Administrator role unless you want them to have full access to your site and its code.
5. Use Intrusion Detection Software
Intrusion Detection Software (IDS) scans your website’s inbound and outbound traffic and notifies you if it detects suspicious activity. With these notifications, you’ll know when and if you need to take proactive measures against RCE attacks.
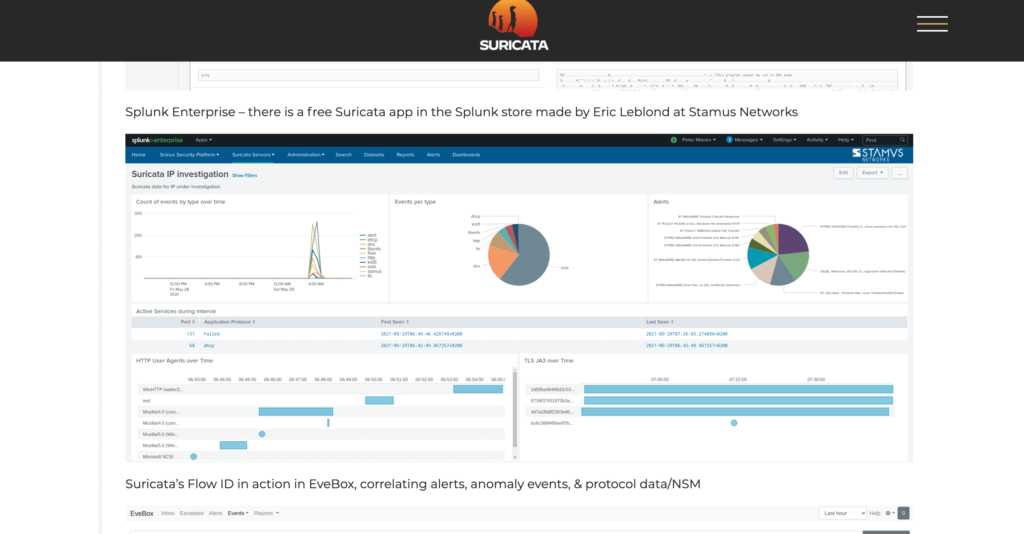
Suricata is an example of a free and open-source IDS tool that can alert you when your network is receiving suspicious requests:
In addition to intrusion detection, Suricata provides services such as:
- TLS/SSL logging and analysis
- HTTP logging
- DNS logging
Suricata also provides users with a full control panel of analytics, events per type, alerts, and HTTP user agents over time.
Conclusion
Keeping your security up-to-date is an essential task as a WordPress site owner. If hackers can access your site and steal customer data, you’ll likely face severe legal and financial penalties. However, you can thwart common cyber-attacks such as Remote Code Execution (RCE) by taking simple precautions.
In this post, we discussed five methods for protecting your website against RCE attacks:
- Install a Web Application Firewall (WAF).
- Make sure your website’s software is updated to reduce security risks.
- Ensure your website is protected against buffer overflow.
- Limit your users’ access permissions.
- Utilize Intrusion Detection Software (IDS).
Do you have any further questions about Remote Code Execution attacks and how to protect against them? Let us know in the comments section below!

No Comments