Sorry to break it to you, but your website is not safe. That’s not necessarily because of something you did but simply because nothing on the Internet is ever completely secure. Every single website faces security threats that can take them down, damage them, or worse.
That’s the bad news. The silver lining is, there are many things you can do to tackle these threats and the first step is to be aware they exist. After all, you can only protect yourself from something that you know could pose a risk.
To help you do exactly that, this article will go over common website security threats for WordPress and beyond. We will talk about what the threats are, how they work, and what you can do to prevent them from happening. When you are done reading, we want you to feel capable of keeping your WordPress website safe and out of harm’s way, so you can focus on what really matters.
Why Care About Website Security Threats?

The first reaction you might have is to ask yourself whether this is even relevant to you. Sure, you often hear about these big data breaches and hacks, but doesn’t this kind of thing usually only happen to large companies? You know, your Facebooks, Twitters, Equifaxes and Yahoos–enterprises that have information worth stealing.
Sorry to burst your bubble, but just because you are not a million-dollar company, there are still plenty of individuals interested in bringing down or breaching your website.
Global cyberattacks increased by 38% in 2022 alone and according to a 2019 Verizon report, small businesses were the number one target, representing 43% of all data breaches. When they become a victim of a cyber attack, it costs these businesses, on average, $25,000. In fact, in 2022, cybercrime damages amounted to $10.2 billion in the U.S. alone, according to the FBI.
However, it’s not just about direct costs of dealing with and cleaning up an attack. You also pay in customer attrition, downtime, work disruptions, loss of trust among customers, being blocked by search engines, and more.
So, even as a small website, you can be a target. That is particularly because most attacks are launched automatically by programs that scan the web for vulnerabilities until they find something. So, if you leave them an opening, someone will try to take advantage of it.
Want to know how to protect yourself? Let’s go over some of the most common security threats out there.
Website Security Threat #1: Phishing
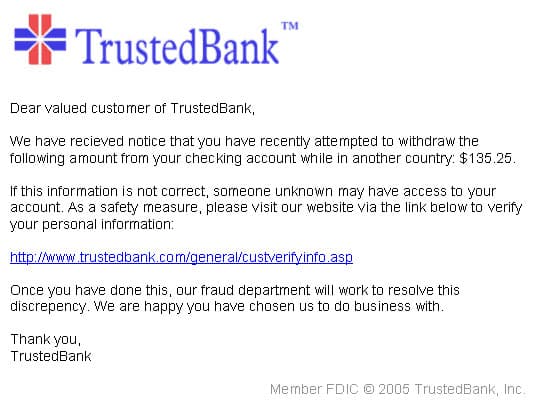
Phishing is when hackers try to get you to visit a malicious website, click on a dangerous link, download a tainted attachment, or give up sensitive information such as your website login. Most of it happens in the form of emails that pretend to be from legitimate sources, however, you can also receive phishing messages via text, messenger apps, or fake social login pages.
Potential Dangers of Phishing
Obtaining your login information through phishing saves attackers a lot of time. Instead of having to painstakingly try to guess and brute force their way into your site, they can simply use the credentials that are definitely working.
With that in hand, they have free reign on your website, especially if the credentials come with high user privileges. They can create new users, add content and links, manipulate files, create backdoors, and even run code. Plus, if you have sensitive information saved on your site, such as customer data in an online shop, a hacker also gets access to that.
Of course, if this happens and becomes public, it’s a real blow to your reputation. Plus, depending on the privacy laws you are operating under, it can come with additional fines.
How to Deal With It
The best way to prevent phishing attacks is to develop awareness for them. If you receive any message asking you for sensitive information, it should immediately give you pause. Don’t send anything back, don’t click on any links, or download and execute the attachments. At the very least, check the sender email address if it’s legitimate. In addition, educate yourself on phishing tactics and do the same with other people in your company.

Website Security Threat #2: (D)DoS Attacks
DoS stands for “denial of service,” which is when someone tries to take down your website by flooding it with illegitimate traffic. The goal is to overwhelm your server with requests so that it can no longer cope and stops working.
DoS attacks are often carried out through botnets, meaning computers that have been infiltrated by a virus or trojan horse and that hackers can command remotely. In that case, you also speak of “distributed denial of service” or DDoS.
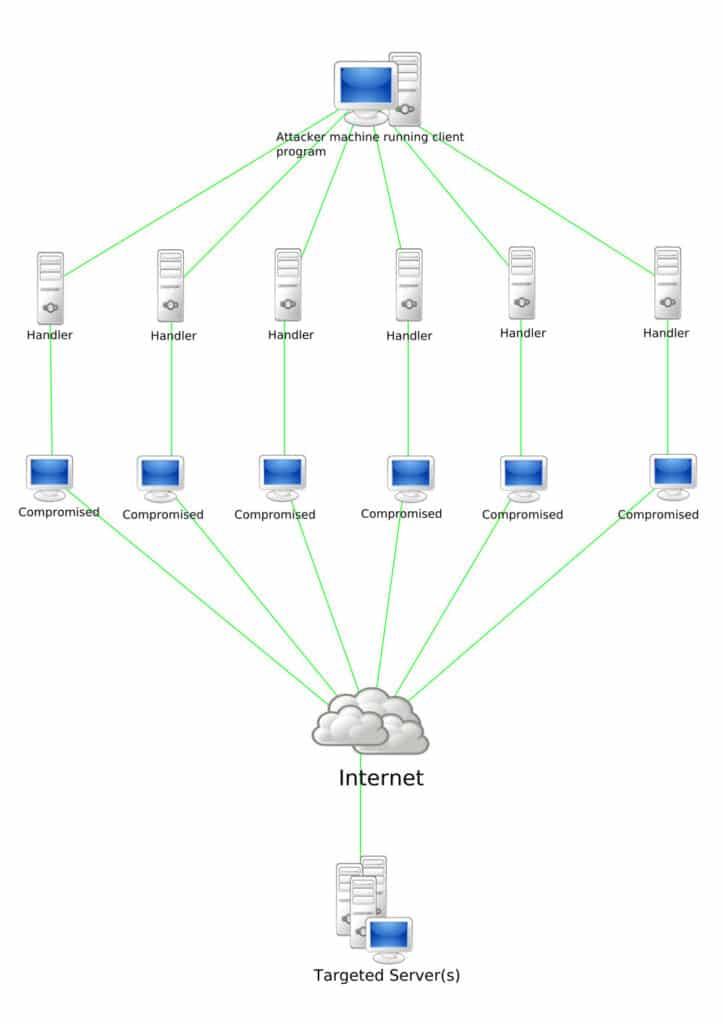
Attacks of this kind are meant to damage a business or website or blackmail them for money. They are also carried out for ideological reasons because the attacker does not agree with what the website in question stands for or because of a public statement a business made. However, in other cases, DDoS attacks can also be used as a diversion to distract you while hackers are trying to break into your site.
What Are the Outcomes?
The effect of a DDoS attack is that the website in question becomes unresponsive and inaccessible for real customers and visitors. The server has too much to do to properly process visits and loads very slowly or not at all for legitimate visitors.
Of course, for most businesses, the website is one of their main assets. When it becomes unreachable, it leads to loss of business and revenue. DDoS attacks can also damage your reputation because some visitors will think your website’s quality is simply not good.
How to Prevent DDoS Attacks
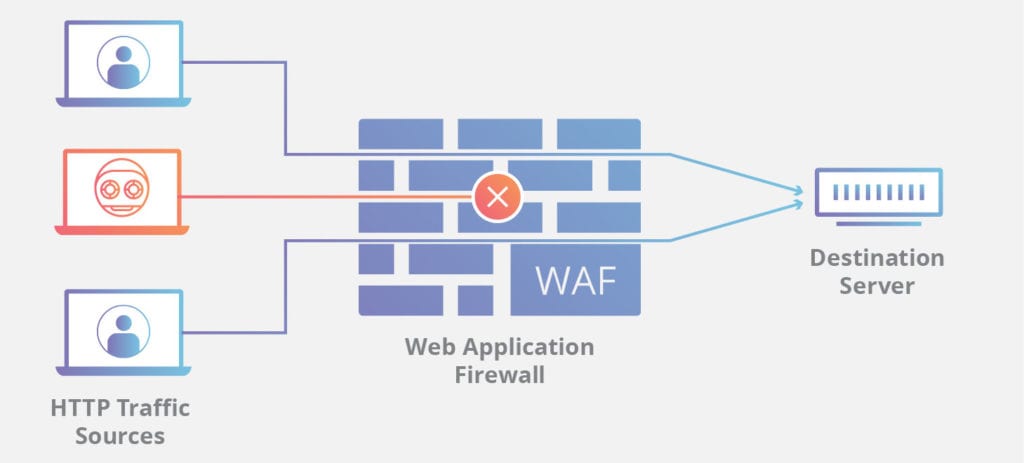
One of the best ways to counteract website threats of this kind is to add another security layer in the form of a firewall or web application firewall. These are designed to filter out malicious traffic before it reaches your site. That way, the attack doesn’t even arrive at your website and can’t do damage. Plus, if the DDoS attack is just a distraction for a break in, firewalls also offer protection for that. Good providers here are Sucuri and Cloudflare.
Another good investment to protect yourself from this website security threat is a content delivery network or CDN. It places copies of your site on different servers, which makes it harder to take it out of the web completely. It can also keep the attack away from your main server. Many CDNs include DDoS protection.
If you host your website at WP Engine, you can take advantage of both of these methods at once by using Global Edge Security. It’s an enterprise-grade performance and security add-on that includes a managed web-application firewall, advanced DDoS protection, and a global CDN. In short, everything you need to keep external security threats at bay.

Plus, it’s pretty hands off. You simply add it to your plan, point your DNS records to the right server, and the rest is taken care of for you. Easy peasy. Finally, it’s a good idea to set up uptime monitoring, e.g with UptimeRobot. That way, you are alerted quickly when your site is no longer reachable so you can take action immediately.
Website Security Threat #3: Brute Force Attacks and Credential Stuffing
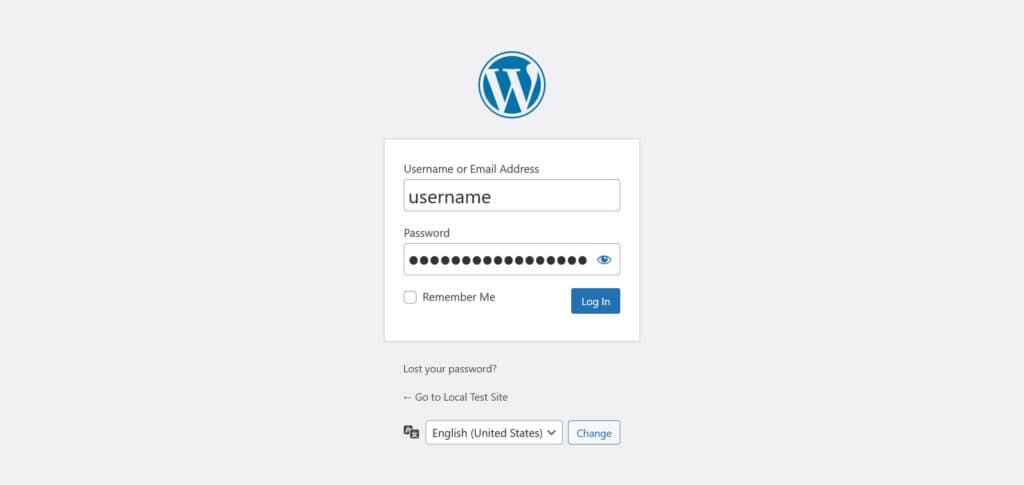
Brute force attacks are somewhat similar to DDoS attacks in that they automatically attack a part of your site. However, instead of blocking traffic, they target your login page and try to get access to the website by guessing your login information. Programs of this kind try many different common password and username combinations per second until they get in.
A slightly more sophisticated variety is so-called credential stuffing. Here, instead of random login information, attackers use email/password combinations that are already known from other data breaches. These attacks bank on the fact that many people reuse their login information.
If an attacker does successfully guess your login credentials, the outcome is pretty much the same as discussed in the “phishing” section.
Deterring Login Attacks
There are several ways you can protect yourself from attacks on your login page:
- Limit login attempts and lock out users that fail too often, e.g. via Limit Login Attempts Reloaded
- Don’t reuse your credentials, have individual passwords for every account you own
- Limit the number of users on your WordPress site and only give them as many capabilities as they need for their job
- Force strong passwords, e.g. via Password Policy Manager
- Better yet, use multi-factor authentication
- Switch off the theme and plugin editor so that attackers can’t manipulate your files from inside the WordPress dashboard
Website Security Threat #4: Cross-Site Scripting (XSS)
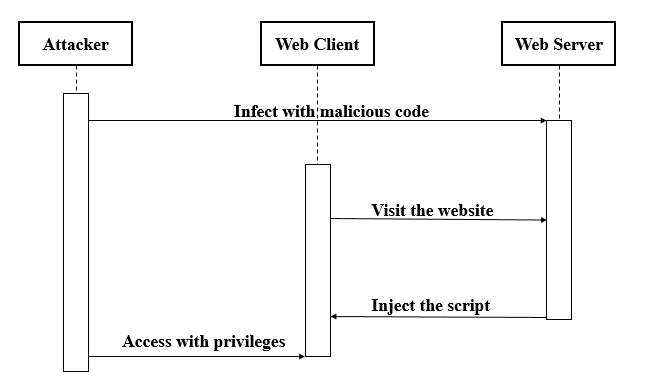
In cross-site scripting, a hacker tricks a website into delivering malicious scripts to a victim’s browser. Because of the source, the browser trusts and executes the script. This often happens through input fields, such as in a contact form. However, the attack can also come from the database of a compromised website.
Possible Outcomes
When successful, an attacker can use cross-site scripting to steal login data, install malware, redirect the user to another site, and even manipulate the page they are viewing. They may also access the website in question as another user and read their data. Plus, they might be able to install software on the victim’s computer.
Overall, cross-site scripting is more of a danger to your visitors than the site itself. However, if it originates from your web presence, naturally, this will not shine a good light on you. Therefore, you owe it to yourself and your visitors to make your site safe.
How to Prevent XSS Attacks
On a technical level, the most important step to prevent cross-site scripting is to sanitize and validate your data inputs. That means denying special characters and symbols to avoid code injection, e.g. make sure that input can’t contain things like script, object or link. Programming languages like PHP and JavaScript offer standard functions for this and WordPress also has its own markup for this purpose.
If you are not a developer, your role is to use good judgment in order to keep code away from your site that doesn’t adhere to these rules. That means, get themes and plugins from reputable sources and make sure that they are well supported and maintained. Plus, don’t install code snippets on your site that you don’t understand.
Website Security Threat #5: SQL Injections
SQL injections are similar to cross-site scripting. They also work by using input fields to run malicious SQL code on your website and gain access to the database.
If your website is vulnerable to SQL injections, an attacker can use this technique to damage it in several ways:
- Create new identities with administrator rights and gain access to your site
- Directly access all data on the server
- Destroy/modify the database to make it unusable
Of course, none of that is good news.
Thwarting SQL Injections
This website security threat requires similar vigilance as cross-site-scripting. Sanitize, filter, escape, and validate data input and make sure you encrypt confidential information. Many web frameworks do this automatically.
As a non-developer, keep WordPress and its components updated and use a WordPress security plugin. Many of them come with functionality to prevent SQL injections. You can find more detailed information on this topic in a dedicated WP Engine article.
Website Security Threat #6: Ransomware/Defacement
Ransomware is a type of software that blocks access to your website or other business assets and only unlocks it again if you pay money to the attacker—and sometimes not even then.

Defacement is similar in that it messes up the design or content of your website or leaves a message of a successful hack on it.
In each case, someone somehow gained access to your site, which can come with a host of negative outcomes:
- The cost of the ransom (if you pay it, which can be expensive)
- Fees for the cleanup
- Lost sales and loss of reputation
- Staff productivity losses from being unable to perform their work
- Reduced search engine rankings due to being blocklisted
How to Protect Yourself
The way to prevent ransomware and defacement attacks is to follow other best practices mentioned in this guide to lock down access to your website and server. Keep your login information safe, your site updated, and put a backup solution in place so you can go back to an earlier version of your site.
Website Security Threat #7: Malware and Spyware
This is not so much a danger to websites themselves but something that can happen to your site. When an attacker gets access to it, they may install malware and spyware that infect your visitors’ computers. Your compromised website ends up acting as a vehicle to further the hacker’s agenda.
What Can Happen?
Malware is a big danger to your reputation. When a browser or antivirus program detects it, they will prevent visitors from accessing your site.
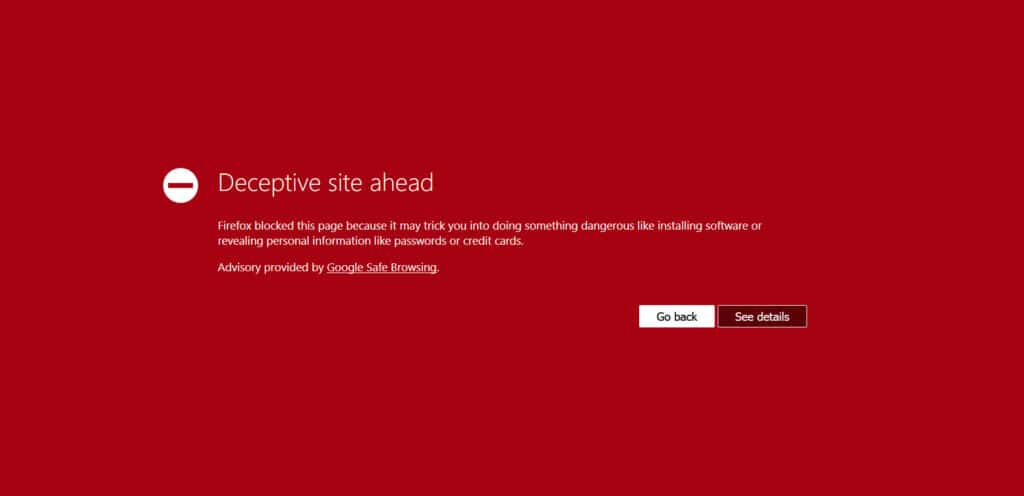
What’s more, search engines can blocklist you and remove you from their index since they don’t want to send their users to websites that harm them.
Of course, both can result in massive traffic loss, and it’s sometimes hard to get yourself off of blocklists even when you have fixed the problem. Without traffic, there is no revenue, no leads, no customers, no business.
Preventing Malware Infections
Again, follow the practices mentioned in this guide to keep other website security threats out of your site. Particularly, employ strong credentials and multi-factor authentication, keep website components up to date, and be vigilant about what you install on your site.
In addition, keep your own computer clean by using antivirus software and regularly scan your website for Malware, for example via Sucuri Sitecheck.
Website Security Threat #8: Man-in-the-middle Attack
These kinds of attacks are common on websites that don’t use encryption for their traffic. Here, the attacker intercepts unprotected data and can thus gain access to login, payment, or other sensitive information. Man-in-the-middle attacks also happen in unsecured wifi networks.
How to Protect Yourself
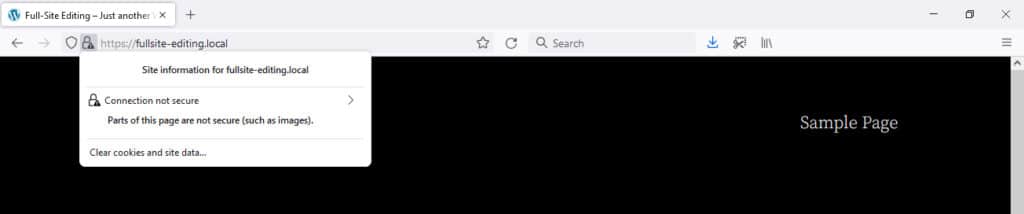
On websites, the number one method to counteract this threat is to use encryption. Install a TLS/SSL protocol on your site and switch it over to HTTPS. This automatically encrypts all information sent between your site and visitor browsers, preventing man-in-the-middle attacks from succeeding.
In addition, protect your work and home wifi with a strong password and by changing the default credentials. Plus, be especially careful when using public wifi. Use a VPN to protect your traffic and only log in to your site from public wifi when absolutely necessary.
Website Security Threat #9: Supply Chain Attacks
A supply chain attack is when an attacker infiltrates a website through third-party software. For example, when someone hacks into an SaaS product that integrates with a lot of websites and then gains access to those sites in the process.
We have seen supply chain attacks in WordPress in recent years. In one case, attackers intentionally spiked plugins with malicious code. Another time, they broke into the distribution server for a WordPress extension to do the same.
In most cases, these attacks were quickly discovered and the plugins in question have been banned or patched. But it’s still something to be aware of.
How to Prevent It
The best recipe for preventing supply-chain attacks is to follow best practices for the use of plugins and third-party code on your website:
- Only use reputable sources for extensions like plugins and themes
- Keep your integrations to a minimum, only install what you really need
- Regularly audit your site if all third-party stuff is still relevant
- Use an activity log to spot suspicious behavior going on on your site
Keep Website Threats at Bay
Security threats are something that every website owner must face. They are an unfortunate reality of operating on the Internet. Thankfully, many of them can be prevented by implementing some common-sense best practices:
- Be vigilant about the messages your receive, links you click on, and attachments you download
- Invest in a firewall, CDN, and uptime monitoring
- Use strong passwords, limit user capabilities and login attempts, and set up multi-factor authentication
- Minimize the amount of plugins and themes on your site and make sure to get them from legitimate sources
- As a developer, sanitize and validate your data
- Keep your website and everything belonging to it up to date
- Use HTTPS to encrypt your website’s traffic
- Have a backup solution in place in case something goes wrong
- Don’t input sensitive information in unsecured networks
Following these should be enough to protect yourself from the majority of common website security threats. Stay vigilant!
What other ways to protect your website from security threats do you recommend? Share your thoughts in the comments below!

No Comments